Nanogirl puts COVID-19 classroom ventilation theories to the test (Video)
The PCB’s (Printed Circuit Boards) – Seeed Studio PCB Manufacture
Soldering Through Hole Components (Video)
Somewhere to save the things I often do but often forget how to do!
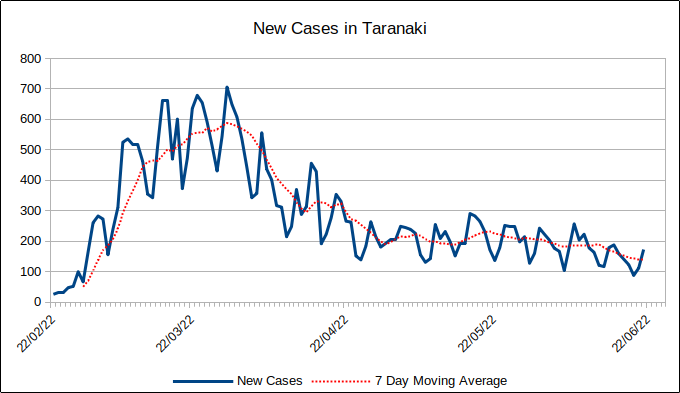
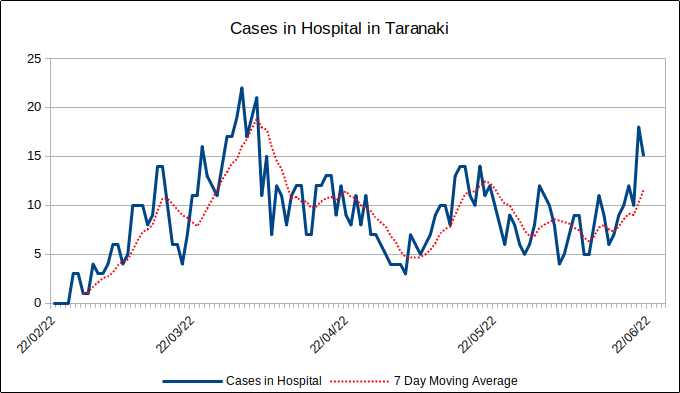
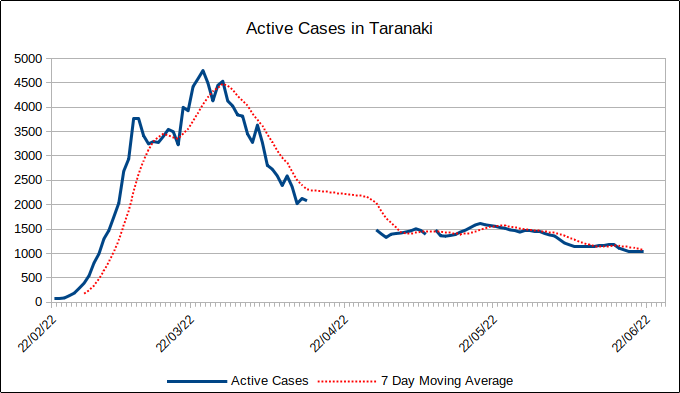
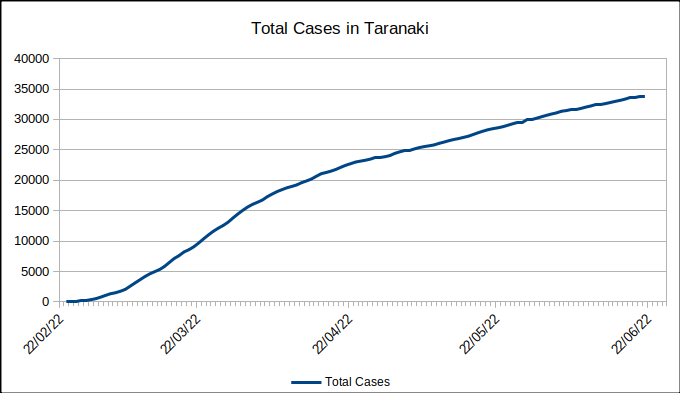
TDHB have stopped publishing data. This data now comes from what is available through Āwhina.
Gaps in Active Cases is due to difficulty locating a data source when TDHB stopped publishing.
Last update 21st June 2022
HC-SR04 Ultrasonic Distance Sensor
How to Use an Ultrasonic Sensor with Raspberry Pi Pico
AliExpress is a wonderful source of cheap electronic components for your projects. If you plan in advance and don’t mind waiting two to six weeks for components to arrive it’s perfect. I have ordered components from many different shops on AliExpress and never had a problem with items not being delivered or as described. A store that I have found to be reliable with a good selection of components is ElectronicFans.
Some people prefer shopping closer to home with Trade Me. A store that I have found to be good is epartners. The items are more expensive than AliExpress but still quite reasonably priced. Items are stocked locally so delivery time is much quicker when compared to AliExpress.
I’ve been looking at a problem with one of my Raspberry Pi projects freezing every now and again. I have a suspicion from reading recent posts that it could be kernel related. I found a good article here which also links to the rpi-update utility on Github here
The great thing here is the utility allows a downgrade.
I can also never remember how to find the current kernel version so, for me, this is what I use:
uname -srvm
I can never quite remember how I like my unattended upgrades configured on my Raspberry Pi’s so I’m just popping it here. It should work for all versions!
nano /etc/apt/apt.conf.d/50unattended-upgrades
Unattended-Upgrade::Origins-Pattern {
"origin=Raspbian,codename=${distro_codename},label=Raspbian";
"origin=Raspberry Pi Foundation,codename=${distro_codename},label=Raspberry Pi Foundation";
};
Unattended-Upgrade::Automatic-Reboot "true";
Unattended-Upgrade::Automatic-Reboot-Time "02:00";
To check it:
unattended-upgrade --dry-run
Logs can be found at:
/var/log/unattended-upgrades/unattended-upgrades.log and /var/log/unattended-upgrades/unattended-upgrades-dpkg.log
This is really just a place for me to remind myself of useful resources I’ve used when undertaking CTF challenges 🙂
Cryptography Resources:
Dcode – the essential site for deciphering and decoding messages
Cryptii – Modular online encoding, encryption and conversion tool
quipqiup – a fast and automated cryptogram solver
Network Resources:
netcat (nc) -a feature-rich network debugging and investigation tool
On a whim I nipped out and bought the only BBC micro:bit in stock at PB Tech in New Plymouth as I was curious to have a play and see where it might fit in between Raspberry Pi’s and Arduino’s for teaching kids.
I thought turning it into a simple digital watch would be a fun place to start learning so, below is the result.
The virtual micro:bits, below, are interactive so click on the ‘shake’ button to simulate shaking it in real life to display the time.
The code can also be found in my Github repo, here. It will be the most recent version if I have made changes and haven’t had time, or have forgotten, to update this post 🙂
Enjoy!
While I was disappearing down a rabbit hole investigating unbound as a DNS Privacy server, I came across Pi-Hole – A black hole for Internet advertisements.
I’ve always used uBlock Origin for ad blocking but that is a per client thing which is a bit of a hassle.
Pi-hole provides ad blocking for all clients on the network, seamlessly. I just configure DNS on each client, via DHCP, to point towards the Pi-Hole server.
Obviously, I love Docker so it’s in a Docker Container on a Raspberry Pi.
Currently, I’ve sacrificed DNS privacy but I’ll work on that later in terms of getting Pi-hole to send all DNS queries through my own DNS server.
This is how I implemented it. Obviously, these aren’t detailed instructions but more of a reference to jog my memory if I need it!
********************
Note: Substitute the IP address of the host that the Container is running on for ${IP} and ${IPv6}
********************
docker run -d \
--name=pihole \
--hostname=pihole \
-p 53:53/tcp -p 53:53/udp -p 80:80 \
-e ServerIP="${IP}" \
-e ServerIPv6="${IPv6}" \
-v pihole_data_1:/etc/pihole/ \
-v pihole_data_2:/etc/dnsmasq.d/ \
--restart=unless-stopped \
pihole/pihole:v4.0_armhf